ZachXBT Criticizes Circle for Inaction During Drift Protocol Exploit
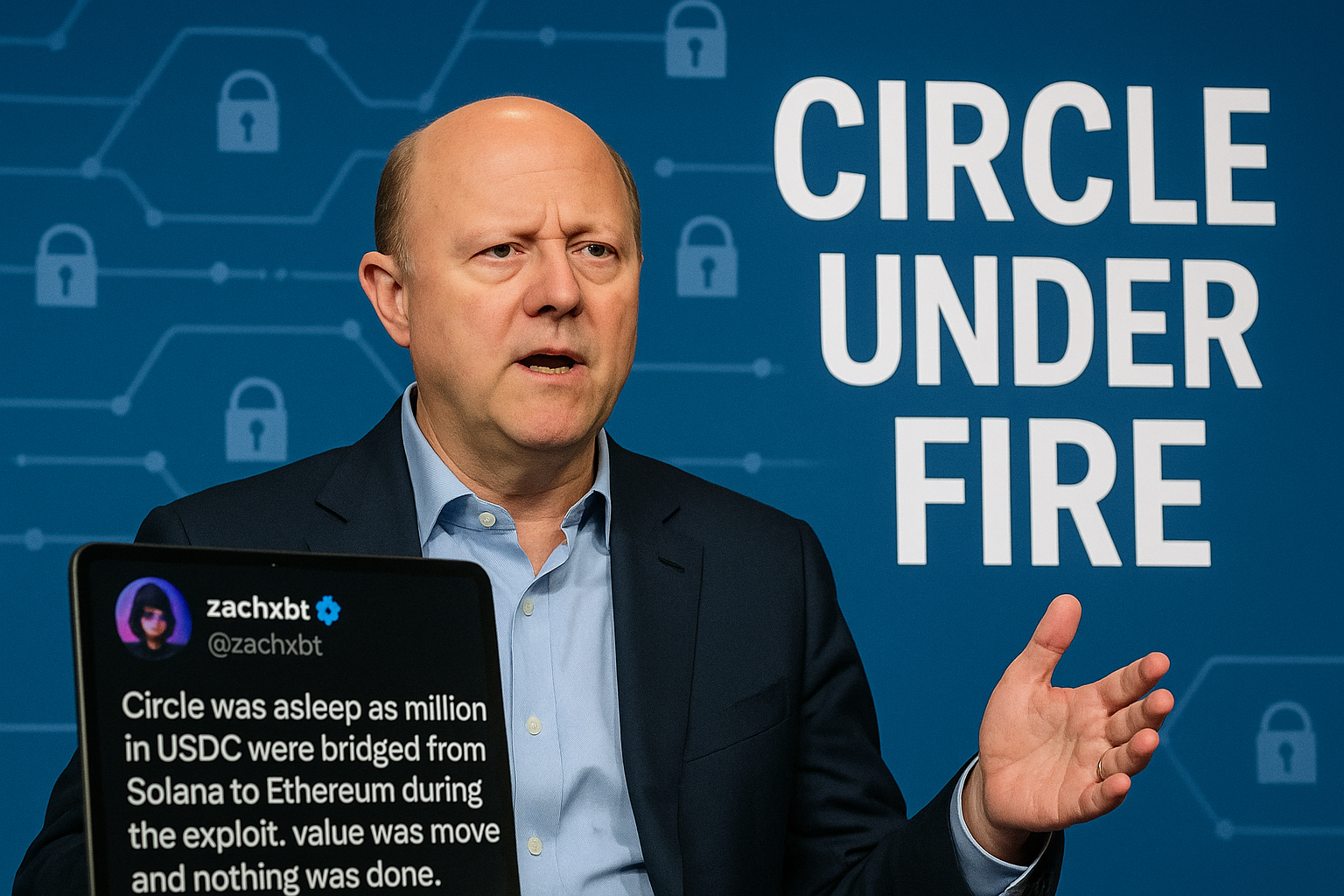
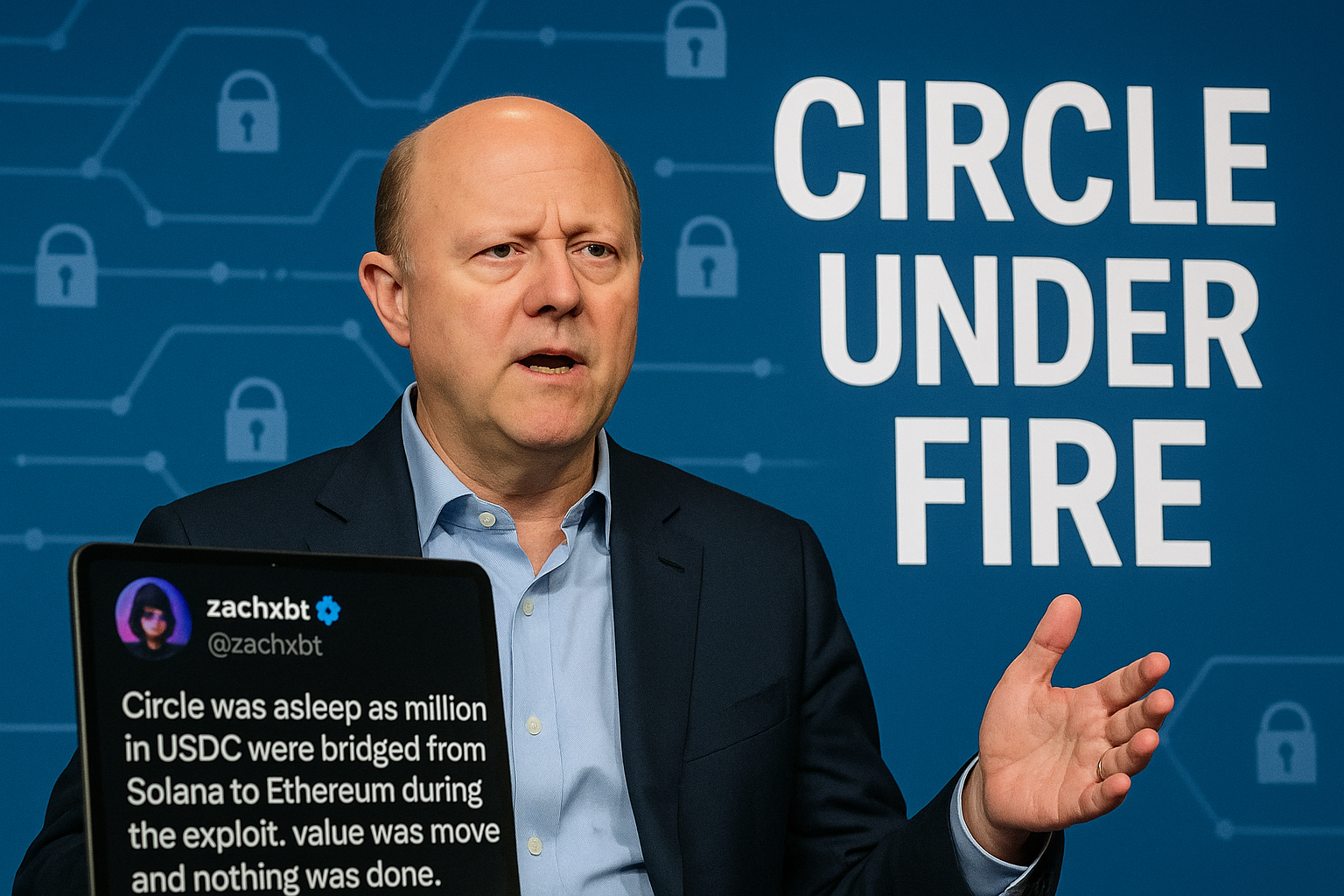
Blockchain analyst ZachXBT has once again called out Circle and its CEO, Jeremy Allaire, for their alleged lack of response during the $280 million exploit associated with Drift Protocol. He characterized the situation as a significant delay as funds were transferred across chains without intervention. In a post on X, ZachXBT asserted that the stablecoin provider 'was asleep' while millions of USDC were moved from Solana to Ethereum amid the crisis. He reported that these transactions were carried out in approximately 100 transfers, stating, 'value was moved and nothing was done.' Additionally, he referenced a recent episode where Circle froze over 16 business wallets, deeming their response 'incompetent' and categorizing Circle and Allaire as 'bad actors' within the industry. These accusations have arisen as market observers have debated whether a swifter response might have curtailed fund movements during the exploit, especially since substantial amounts were allegedly transferred over several hours without any stoppage. Meanwhile, Drift Protocol clarified that the incident was the result of a highly orchestrated and sophisticated attack rather than a vulnerability in their smart contracts. They explained that the attacker gained unauthorized access through a 'novel attack involving durable nonces,' which allowed pre-signed transactions to be executed later. This enabled the attacker to circumvent real-time detection and rapidly seize administrative permissions linked to the protocol's Security Council. Drift confirmed the exploit was not due to compromised seed phrases or coding flaws but involved unauthorized or misleading approvals likely acquired through social engineering. The attacker managed to obtain the necessary 2-of-5 multisig approvals and executed a malicious admin transfer in a matter of minutes, subsequently introducing a harmful asset and lifting withdrawal limits. The timeline released by Drift indicates that the groundwork for the attack commenced as early as March 23, with the establishment of durable nonce accounts related to both legitimate multisig members and wallets controlled by the attacker. Preparations extended through a multisig migration on March 27 and additional nonce activities on March 30, culminating in the execution phase on April 1, coinciding with the triggering of pre-signed transactions shortly after a valid test transaction. In response, Drift has frozen remaining protocol functions, excluded the compromised wallet from the multisig, and initiated collaboration with security firms, exchanges, and law enforcement to trace and potentially recover the stolen assets.

Leave a Comment